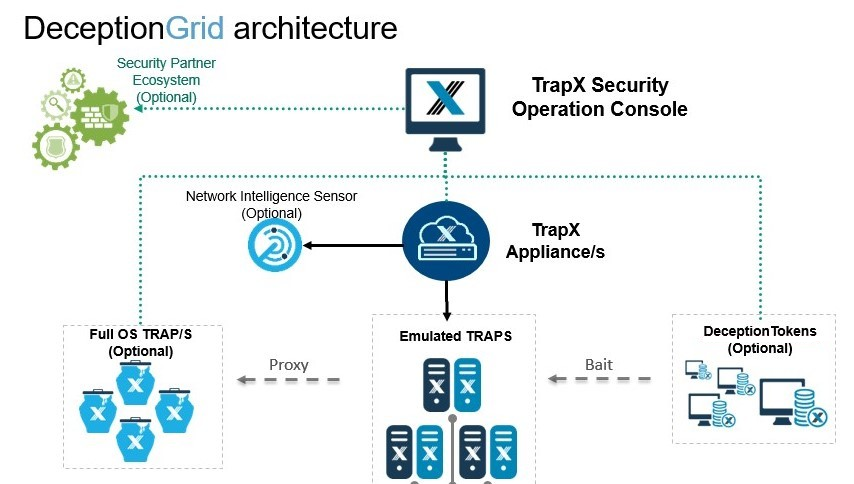
B2B-Solutions implemented the country’s first TrapX Deception Grid deployment.
This honeypot-like solution contains:
- TSOC (TrapX Security Operation Console) – the “brain” of the system. This is the central management console, where we configure, deploy the solution, and do all our daily job. Since this is a web service, it can be deployed anywhere – on-premise, in the cloud, or in the MSSP environment.
- TrapX Appliance (TSA) – a virtual server where all our network sensors (or traps) actually “live”. It can be connected to the network with ordinary access ports, or trunks if we want to monitor several subnets at once.
- Application Traps (Full OS) – traditional Windows-based “honeypots”. We don’t need a lot of them since the main job of these servers is to provide IT services to the next level of sensors or to attract attackers to fake application servers.
- Emulated traps – the main component of the solution, which allows us to create a very dense “minefield” for attackers and saturate the whole enterprise network with our traps. The attacker sees such a trap as a real Windows PC or server, a Linux server, switch, or other devices that we have decided to show him.
The combination of these two technologies (FullOS and emulated traps) makes it possible to achieve a high statistical probability that the attacker will eventually, sooner or later, collide with some element of our alarm network.